PHP Serialization has a fatal flaw which allows for pollution of the scope and global context of an application, as well as running arbitrary code in some scenarios if sources of taint are allowed in. It is a very high impact attack but requires in-depth evaluation criteria and careful inspection to be caught.
I have prepared a lab to explore and try this attack, available at:
PHP Serialization Pollution Lab
Give it a try and let me know what you think. I suggest you do a lot of debugging on the code and master its exact running flow. Don’t forget that the source code of that page is available at:
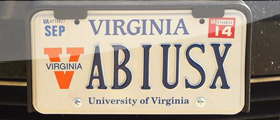
https://abiusx.com/lab/hacking/serialize.src.php
I’m gonna describe this with details in a much later date.
4 comments On PHP Serialization Pollution Attack
My solution :
we send this serialized data to overwrite sessions through the __destruct() function:
O:14:”PasswordSetter”:2:{s:8:”username”;s:5:”admin”;s:8:”password”;s:4:”1337″;}
Afterward we can login with “admin” username and “1337” password.
please fix this page :
PHP Serialization Pollution Lab(404 NOT found ERROR)
Apparently because of the new website structure I can’t :D It poses a security risk!
can u please share the source
Sliding Sidebar