This post is about Sharif CERT (APA) center’s recent CTF (10 dec 2012), which is one of a kind in Iran. Most CTFs are a few days long since there are time-zone differences, but since this one is in Iran, its only a few hours long and full of pressure.
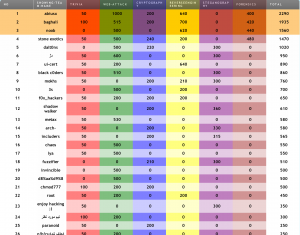
Also it is fairly general purpose, with Trivia, Web Hacking, Cryptography, Steganography, Reverse Engineering and Forensics amongst it genres. There’s also the final scoreboard of the contest. As usual, team AbiusX nailed this CTF, though this was the initial round and the main round is held inside Sharif University of Technology in Tehran.
APA CTF usually pisses me off, as some questions are not technical and more of a puzzle than a question – as you will see soon – and also because the guys in charge of making up questions have a very poor English (rofl). But it’s getting much better over the years and this version was perfectly acceptable, specially the parts about segmenting different teams’ flags.
There were 2 trivia questions, 4 web flags, 2 reverse engineering flags and the rest each had one flag. Genre scores were 100 for trivia, 1200 for web, 200 for crypto, 600 for reverse engineering, 300 for steganography and 400 for forensics, plus bonuses for quick solvers.
The Questions
This section will describe each questions, its strengths and weaknesses and the solution to it.
Trivia
The first trivia question was “The tool that Microsoft uses to detect security vulnerabilities in it’s development.“. Answer was of course SAGE (which obviously we couldn’t figure out). In my 5 years of active OWASP involvement, Microsoft is the leading company that benefits from OWASP research and development, without even admitting it. Many open source initiatives (like Mozilla) are reluctant to turn towards OWASP without some bragging.
Second trivia was “Malware that asks for money to remove itself.“. These are getting a place in malware world, and are known as ransomware.
Cryptography
The cryptography challenge really crawled up my ass all the way up my brain, as it was a puzzle and not a cryptography challenge. You might know that I’m a crypto nerd, and I’m deeply into advanced number theory, information theory and everything cryptography. When you opened the question link, you would face this:
Now, since there are no plaintext and no hints, this would either be a classic easily-breakable classic cipher, or some sort of encoding (which APA guys generously confuse with encryption). Most classic ciphers operate on alphanumeric inputs and provide alphanumeric outputs, except for a handful (Polybius, Straddling, Bifid, etc.), and that bunch produces a reduces number set (i.e not all numbers are used in the result).
I quickly wrote a code to decrypt all the ciphers I knew to use numerical I/O, and ran it on the numbers above; all resulted in gibberish. Then I inspected the numbers for a while, its 2046 characters long, which is 2x3x11x31, and oddly odd combination of primes; so I factored this string into its prime factors in a 4D manner, still no sense.
Now I thought maybe it is a commonly known sequence, so I asked my friend Google about it, and it said no results (keep in mind that i copied first 24 characters). Then I ran some analysis using a bunch of tools on the sequence, namely Index of Coincidence, Frequency Analysis (up to 32 letters!) and finally Entropy Analysis. Entropy analysis yielded high entropy, thus the sequence could not be a classic cipher. All classic ciphers have somewhat weak Diffusion and Confusion, so they do not increase the entropy.
Side Note for Crypto Newbies: An ideal cipher is like a machine, that receives a ball from you, and outputs some dust. Then when you pour the dust back into the machine, it gives you a ball. In a more technical manner, it increases the information entropy to maximum, so it’s similar to noise; but it has a unique way of turning it back into something structured. To put it in simple words, if you zip a maximum entropy data (like something encrypted with AES), the zipped data would have approximately the same size (since it has no detectable pattern).
But if the sequence was a new cipher, there would be no way to crack it! Not without some plaintext, hints, and some parts of a key. So I just left the question be.
Solution. Later a hint popped up in news section, saying 3.14. I thought they mean it is 3:14, and not much of the contest is left (I’m too much of a nerd). Later I figured out it’s 3.14 (Pi number), then I searched around and found that this sequence is very similar to extension of Pi number. You must know that Pi number has a sequence with no pattern, and thus the entropy theory. Then I figured out that the sequence is not exactly the Pi number’s decimal part, so I did a quick code to list out the differences, which were (they might’ve been different for other teams):
79 55 1 110 70 52 114 99 65
Now I concatenated these, and entered as a flag, which was rejected. No hint was given to me on what else to do, so I assumed that people in charge have made another mistake, and remove the number “1” from the result sequence, and then converted each ASCII code to its corresponding character, which was the correct flag.
You might ask why the googling did not yield any result, it was because 21st and 22nd letter were injected and were not original Pi number.
Steganography
The link to the question, provided you with an image:
 Now initial analysis revealed that this is a 256 color Bitmap file. Since I’ve done a few bitmap editors when I was around 12, I know that 256 color bitmaps have a palette in their header that lists 2^8 colors out of 2^18 possible colors (6 bit for R, G and B). I inspected the palette, no obvious pattern. I inspected the colors, no LSB data. I ran every stegano tool I could find on the image, all failed.
Now initial analysis revealed that this is a 256 color Bitmap file. Since I’ve done a few bitmap editors when I was around 12, I know that 256 color bitmaps have a palette in their header that lists 2^8 colors out of 2^18 possible colors (6 bit for R, G and B). I inspected the palette, no obvious pattern. I inspected the colors, no LSB data. I ran every stegano tool I could find on the image, all failed.
Then there was a hint in the news section : “Focus on hot theme colors.”. What colors are deemed hot? Later I found out that they mean red variations. Then I filtered the image so that only red colors remain and all look alike. I looked deeply at the image, rotated it at every angle, and the only thing I could see was something similar to sport logos (the ones that show a man swimming or playing basketball in TV news programs).
Solution. We did not nail this particular question, as it had absolutely nothing to do with science and technique. It was a brail text converted to an image.
Forensics
The question provided me with a 16mb 7z file, presumably a physical memory dump image of a system. Now what we were supposed to find in it, was yet another question never answered. The biggest problem with APA questions is that they do not clearly state what you should look for, though in real life you always know what ends you’re pursuing.
When trying to decompress the file, usual decompressors would argue that it is corrupt. Later I found out that it could only be unzipped by 7zip software (namely 7za executable as I don’t live inside a Windows system). Now we had a 68 MB file, with no absolute idea as to what to search for in it (68MB is a little too much).
Later a hint came up, telling that it is intended to be inspected by the Volatility software. I obtained the software, which is in Python. Ran it, it required a bunch of libraries from Google Code. I fetched those too, and ran the tool. It had unlimited options.
The image belonged to Windows XP SP3, list of processes showed usual Windows components, as well as two cmd.exe. Now we could dump the console commands typed in those cmd.exe files via the memory image, so I did. They had renamed a CTF3.exe file into conhost.exe and ran it.
I dumped the memory image of the conhost.exe file into a real file (executable files are loaded into memory before being executed). Ran it on Windows:
‘conhost’ is not recognized as an internal or external command, operable program
or batch file.
Error reading registry key!
Inspecting the executable file with some debuggers, revealed that its looking for for Registry Key “Keyboard Layouts\Preload” in HKLM. Now I went there in my Windows machine, and nothing particular was there. Then I dumped the registry value for that key inside the image file (Windows registry is alos loaded into the memory), and the flag was there, fairly easy.
The problem was, why the hell would a forensics guy want to check up a stupid common registry key in some memory image?! The philosophy behind the question bugged me greatly.
Reverse Engineering
We were provided with this zip file, which included a readme.txt, a reverse.exe and a libeay32.dll. Since I was an OpenSSL freak, I knew that libeay32.dll belongs to OpenSSL, so the program is presumably using some AES, RSA, or other nasty OpenSSL functionality (you would know what I mean if you worked directly with nasty OpenSSL code).
Readme.txt stated that Executable is currently configured to generate flag2 for “SharifCERT”. You should generate and submit flag2 for “Team02”. Inspecting the executable resources revealed a “SharifCERT” string amongst them. Replacing it with Team02 and running the code, gave the first flag, which we got in a few minutes after the beginning of contest.
Now for the second flag, some anti-debug features were implemented into the executable file. Finally it became obvious that it references some memory in libeay32.dll file, that is not there. After lots of hours of headache, we figured out that the libeay32.dll opened in the debugger, is actually the one loaded by the operating system earlier, and not the one in executables folder (people unfamiliar with the way Windows handles Dynamic Libraries, just know that is does a very poor job of that).
Replacing it with the file in folder, revealed the second flag in that memory spot.
Web Hacking
There were two web challenges, one with 3 flags and 1000 score points, PHP MySQL based, and one with 1 flag and 200 score points, added for the sake of those newbies that can only hack ASPX. Unfortunately the second one had a bug which prevented our team from nailing it, as I’ll describe very soon.
The first challenge, had the chase your own tail problem, which was frequent on the contest. You had no idea what they expected you to do, and you were faced with a vast web application, with really nasty code – very hard to keep inside your head – and poor English text.
There were four initial pages, a homepage welcoming you, a css page which showed you a copy/pasted page, a downloads page which provided 3 links to download stuff, and a final page asking for email and password to login, with a link to another page asking for valid email to reset password.
The download page referenced a /includes/downloader.php file which accepted a GET parameter, namely file, which itself accepted the base64 encoded string of the filename’s reverse. For example to download css.html, you had to base64encode lmth.ssc. This code does exactly that:
<?php die(base64_encode(strrev(“filename.here”)));
Unfortunately, the downloader script would not work correctly with files containing .. and / in their address, so no LFI/RFI. It would just say “File not found”.
There was another interesting file mentioned in the css page, namely /includes/css-parser.php which accepted raw GET data, in the form:
css-parser.php?extension,filename1,filename2,…
And would dump the contents of filename1.php, filename2.php and the rest (if provided). Unfortunately, it only allowed you to peek at files inside /includes/ folder, as it had:
$file = preg_replace(‘/[^a-zA-Z0-9\_\-\/]/’, ”, $file);
$output .= file_get_contents(dirname(__FILE__) . ‘/’ . $file .’.’.$type) . “\n”;
So, we took a look at downloader.php:
/**
FLAG: lol-first-key!.php
**/
$filename = $_REQUEST[“file”];
$filename = strrev(base64_decode($filename));
$filename = str_replace(‘..’, ”,$filename);
$filename = str_replace(‘backups/’,”,$filename);
$file = ‘../files/’.$filename;
if(file_exists($file) && !is_link($file) && !is_dir($file))
Now the first section which states the flag file, was mistakenly typed as “FLAG: lol” when I first encountered this file. I was amazed at what it could mean, and they never told me. Later they fixed it so I did not get quick-solver’s bonus for this.
The code segment uses blacklist filtering, and if you’ve followed what I say at OWASP PHP Security Cheat Sheet (and any other security related article), you’re bound to be pawned if you use that. You should use whitelist filtering, i.e only allowing what you know is safe, and not filtering what you know is unsafe. This code, filters double dots and “backups/” strings, then prepends “../files/” to our input. That’s why we could neither use .. nor use slash in our addresses. Now pawning that is as simple as providing it with:
.backups/./index.php
Now it first checks for double dots, non found, then replaces our “backups/” with nothing, turning our input effectively to “../index.php“. This can never be prevented, even if you put this filtering code inside a while loop. Index.php had:
require_once ‘includes/main.php‘;
…
Now the main.php file was interesting, but you couldn’t read it because it had the protection string on its first line. The trick was easy, simply provide css-parser.php?php,downloader,/main so that you get a concatenated output of both files. Main.php referenced a bunch of useful files:
require_once ‘includes/master.auth.php‘;
require_once ‘mysql-config-files/config.inc.php‘;
require_once ‘mysql-config-files/config2.inc.php‘;
require_once ‘classes/mysql.class.php’;
require_once ‘classes/auth.class.php‘;
require_once ‘includes/password-recovery.php‘;
Now the two interesting files were mysql config files. Hints in the news told us that MySQL port is open from the world, so using the mysql client and the credentials in the file, one could connect to the server, list emails and passwords and even add an email and use forgot password, then login with it and get the 3rd flag (500 scores).
The second web challenge, required you to use SQL injection on ASPX server to get into admin.aspx, and read some files via the admin panel and decrypt them to see the flag. Unfortunately the login screen had a bug which caused it to pop an error all the time, regardless of being a wrong password or an actual error. I bypassed it using Soroush’s method on ASPXERRORPATH and also found the admin.aspx myself (which didn’t require login), but since it was buggy, I left the question be. Again, nobody told me that it was fixed so I never returned to it.
Conclusion
Generally, the contest was fairly straightforward and cool, and I and the rest of participants liked it. APA needs better guys on crypto and stegano challenge design, but it’s acceptable for now. Please drop comments about your ideas about this writeup and the contest in general.
5 comments On APA CTF 2013 Write-up
Congratulation,
Wish to see you on top every time. :D
But about steganography question, is there any mechanism to solve it?
please correct the Reverse
first flag was inside the reverse.exe as plaintext.
flag 2 : the base64 encoded “SharifCERT” was at rsrc section of libeay32.dll
we changed them to base64(Team02) and run…
جالب بود.من هم در مسابقه بودم.البته بار اولم بود و خیلی خوشم اومد از مسابقه.بی صبرانه منتظر 24 بهمن هستم.
پسرم جی آر ای چه کردی صبح امتحان جی آر ای با دوستت دیدمت که به نظر میومد اوضاع خوبه نمرشو که نذاشتی 90 درصد یعنی چه آخه؟شرمنده کامنت به پستت ربطی نداره
Pingback: CTF is online for everybody | Yashar shahinzadeh official blog ()
Sliding Sidebar